Three containers on MSC IRINA. Two bills of lading. Somewhere in the Gulf of Aden. And the last position update you got was a carrier email - six hours old - that said “vessel proceeding as planned.”
That was the phrase, wasn’t it? Proceeding as planned. Right up until a Houthi missile landed close enough to reroute every vessel in a 200-nautical-mile radius and your customer called asking where their shipment was.
You didn’t know. Not because you’re bad at your job - but because your cargo visibility system was a shared inbox and a spreadsheet someone updated when they remembered to.
The gap nobody talks about
Here’s what I’ve noticed after 20-plus years running supply chain operations in a multi-country aspect: the gap between “a crisis happened” and “my cargo is affected” is where all the damage lives. Not the crisis itself. The gap.
During the Red Sea disruptions, the big digital-native industrial companies - with their visibility platforms - pivoted fast. They had real-time vessel tracking. They had automated rerouting alerts. They had dashboards.
Everyone else had a PDF from the carrier and a WhatsApp group.
And the enterprise solutions that promise to fix this? They cost, they take months to implement and often require an IT team. For multinational companies this is necessary because the complexity and interdependency of systems and stakeholders is huge. But what about mid-size business?
Most mid-size companies without such resources just... absorb the risk. They call the carrier. They check Marine Traffic manually. They wait.
That sets a scene for experiment Nr. 1
What I built
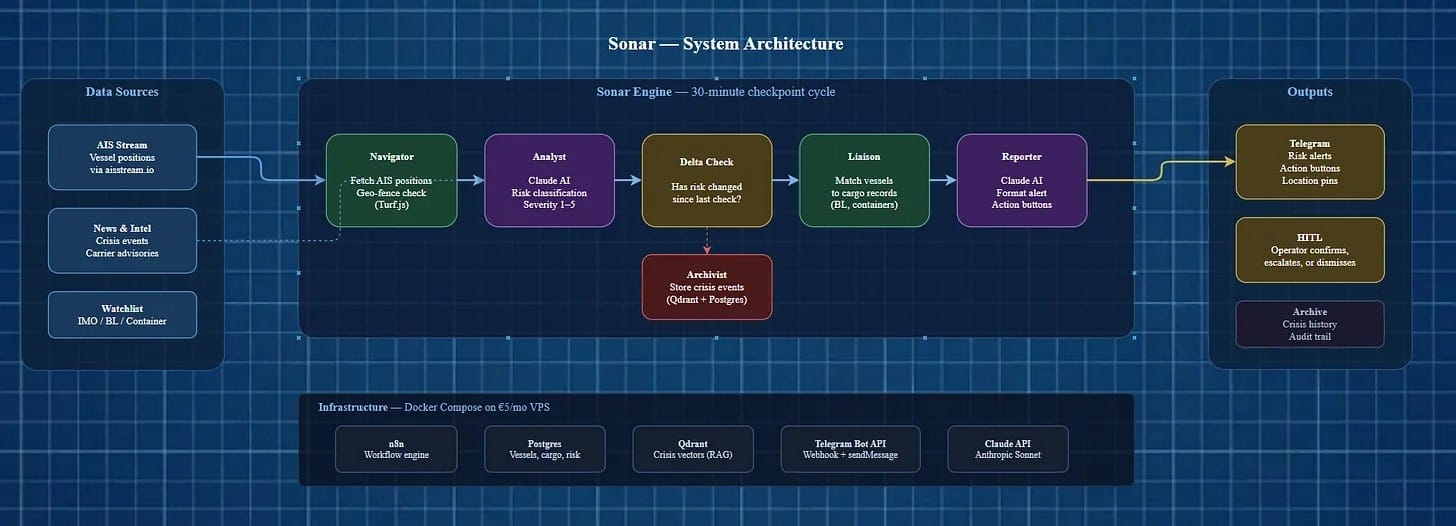
Sonar is a cargo risk monitoring system that does one thing well: it tells you when your specific cargo is in danger, before you find out from the news.
Five AI agents. A 30-minute monitoring cycle. Vessel positions cross-referenced against geopolitical risk zones, matched to your actual bills of lading and container numbers. Alerts land on Telegram with action buttons - confirm, escalate, dismiss, snooze.
The whole thing runs on a single VPS. Five euros a month.
I built it over a series of weekends. n8n handles the workflow orchestration. Claude’s API does the thinking. Postgres stores the data, Qdrant handles vector search, and Telegram is the interface. No frontend. No React app. No login page. Just a bot that messages you when something matters.
It’s not a prototype. It monitors real vessels in real risk zones right now.
How the 30-minute cycle works
Every half hour, Sonar runs through a pipeline. Five agents, one after another. I’ll walk through what each does - but fair warning, they’re not all equally interesting.
Navigator is the simplest. It fetches the live AIS position for every vessel on your watchlist - AIS being the GPS of the maritime world, every commercial vessel broadcasts it - and checks whether that position falls inside one of five geo-fenced risk zones. Turf.js polygon math. Is the vessel inside a danger corridor? Yes or no. That’s it.
Analyst is where it gets good. This is Claude reading the room. It takes the vessels that are inside a risk zone and assesses the actual threat - not “vessel in Red Sea, send alert,” but: What’s happening in this region right now? What’s the severity? Is this a piracy threat or a port closure? How reliable is the source? I spent more time tuning this agent’s system prompt than building the other four combined. The difference between a useful alert and a noisy one lives entirely in how well the Analyst reads context.
Delta Check is one line of logic that saves the whole system from being annoying. It compares the new risk score against the last one. If nothing changed, the pipeline stops. No alert. Nobody wants 48 messages a day saying “still in the Red Sea.”
Liaison matches the at-risk vessel to your cargo records - bills of lading, container numbers, destinations, ETAs. This is the step that turns “a vessel is in a risk zone” into “your two containers with electronics bound for Hamburg are on a vessel in a severity-4 zone.” I’ve been in enough crisis calls where someone asks “but which of our shipments is actually on that vessel?” and nobody knows. Liaison knows.
Reporter formats everything into a Telegram message. Severity emoji. Vessel name. Risk delta. Cargo count. Recommended action. Inline buttons. Done.
Then it waits for a human to click a button. The response gets archived - Postgres for the audit trail, Qdrant as a vector embedding so the Analyst can reference it later. Backend engine is powered by N8N logic to balance the tokens consumption:
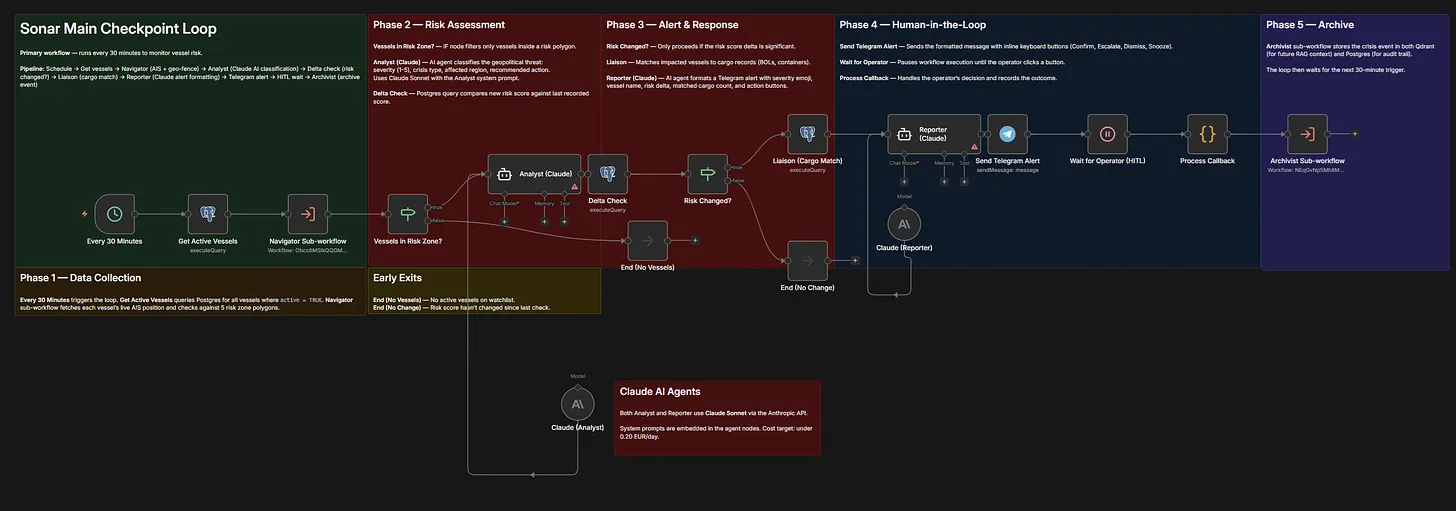
The entire cycle takes about 15 seconds. The AI calls cost fractions of a cent. The operator never opens a dashboard, checks an email, or logs into anything.
The interface nobody needs training for
I spent a long time in my career watching expensive software deployments fail not because the software was bad, but because the people who needed to use it... didn’t.
The Excel loyalists. Month three of any implementation, you find out who’s actually using the tool and who’s working around it. Telegram changes that equation. Every ops person already has it on their phone. There’s nothing to install, nothing to learn, no credentials to manage.
Here’s what it looks like:
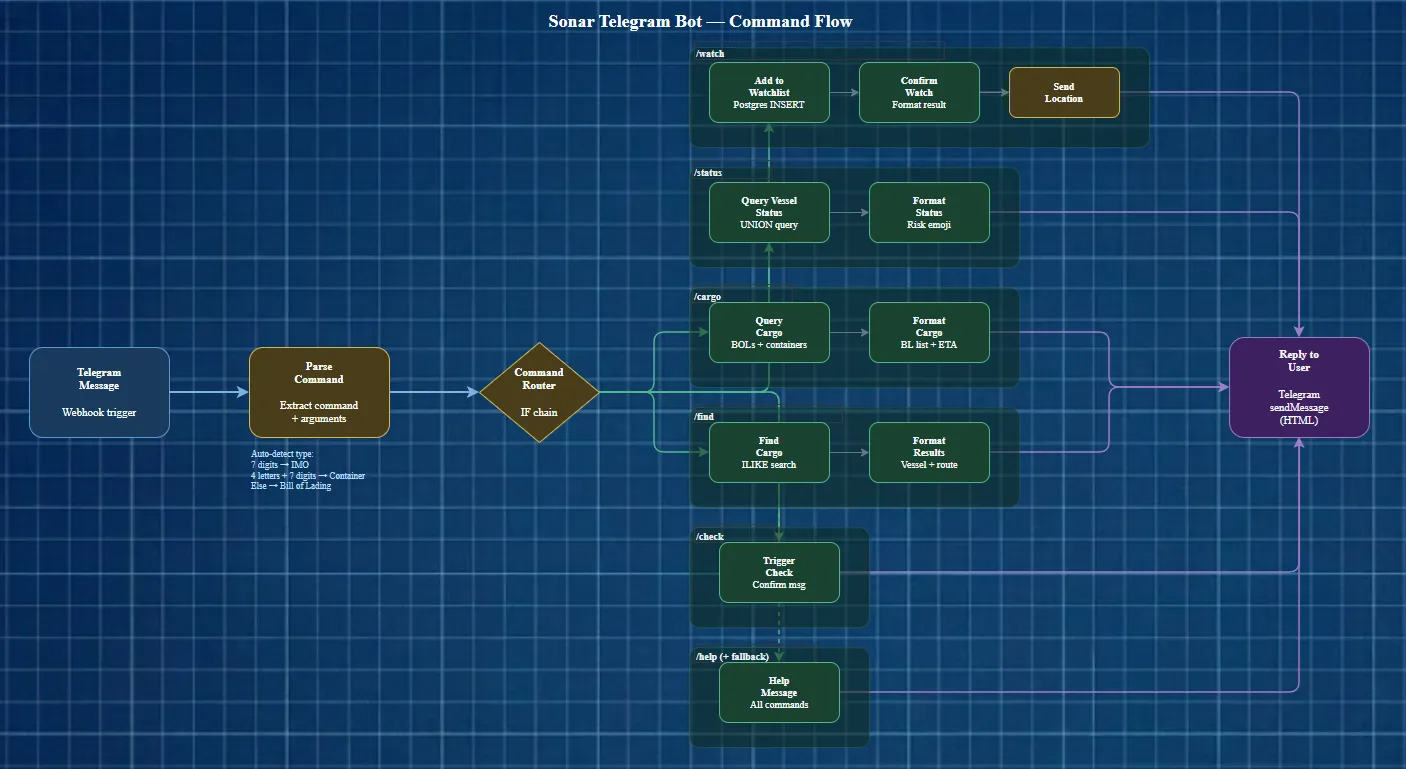
/watch 9334562
That’s it. Seven digits - the vessel’s IMO number. Sonar looks it up, adds it to the watchlist, and replies:
Sonar - Vessel Watched Vessel: MSC IRINA (IMO: 9334562) Operator: MSC Status: Active monitoring Sonar will alert you if this vessel enters a risk zone.
Plus a map pin showing the vessel’s last known position. Gulf of Aden, 12.48°N, 45.02°E.
Don’t know the IMO? Use a container number:
/watch MSCU7234561
Or a bill of lading reference:
/watch BOL-2025-GULF-001
Sonar auto-detects the type. Seven digits is an IMO. Four letters followed by seven digits is a container. Anything else is a bill of lading. No dropdowns, no forms, no “please select watch type.”
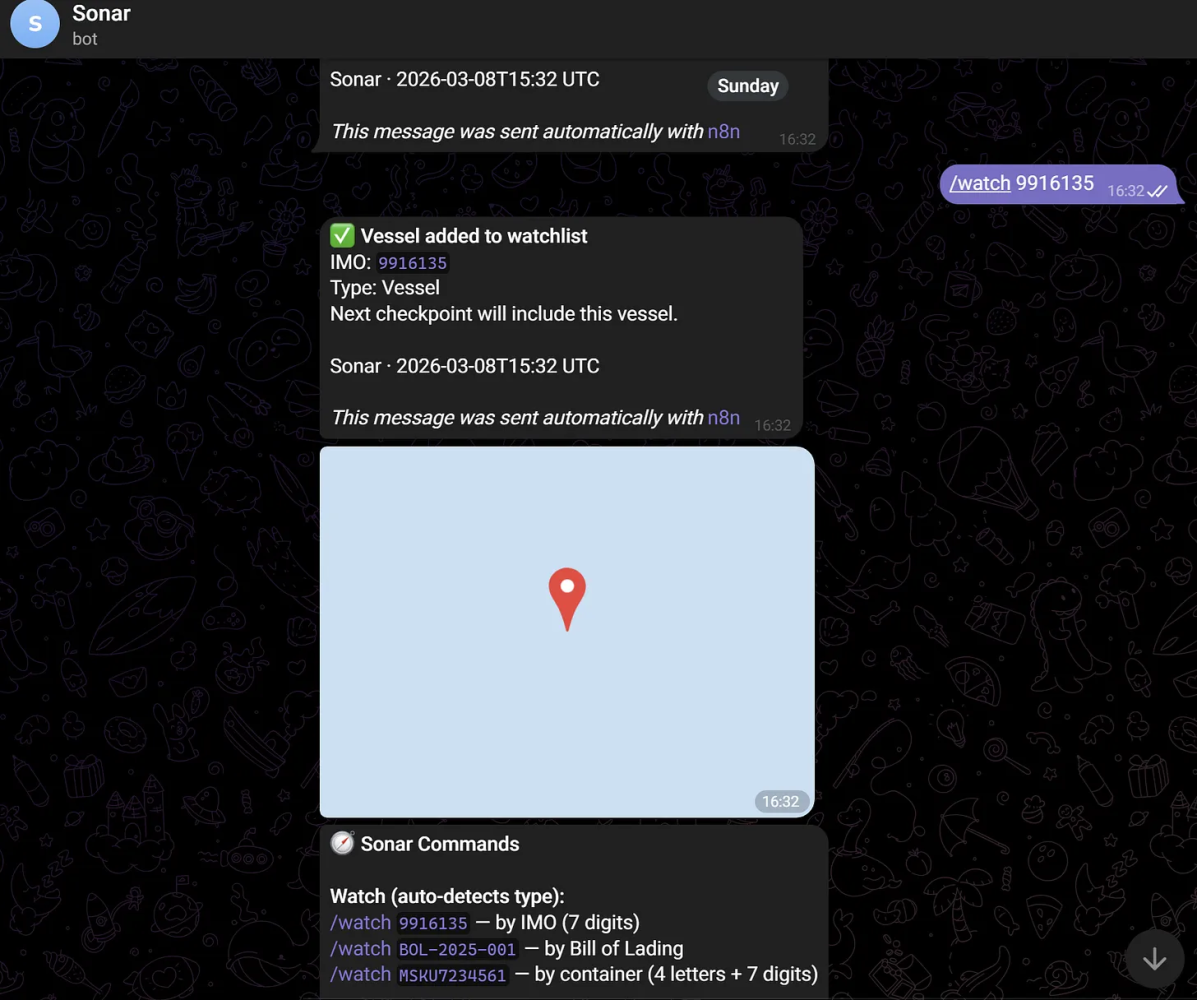
Six commands total:
/watch <ref> Add vessel, container, or BL to watchlist
/status See everything you’re monitoring with current risk
/cargo <IMO> List all cargo on a specific vessel
/find <ref> Search for a container or BL across all vessels
/check Trigger a manual risk checkpoint
/help Show all commands
Why AI, not rules
A rules engine would be simpler. Vessel in polygon, send alert. Done.
But here’s the problem: not every vessel in the Red Sea is at the same risk. A Maersk container ship transiting at full speed through a well-patrolled corridor is in a fundamentally different situation than a smaller vessel anchored near the Yemeni coast. A rules engine can’t tell the difference. It treats them both like a fire alarm going off - same volume, same urgency, same message. That gets old fast.
The Analyst agent uses Claude to read the actual threat context:
- What type of crisis is active in this region right now
- How severe - a distant missile strike vs. a direct shipping lane closure
- Whether the source is verified, probable, or unconfirmed
- Whether a carrier advisory has been issued
- Historical context - has this type of event escalated before?
The output isn’t “danger” or “safe.” It’s structured:
{ “crisis_type”: “missile_attack”, “severity”: 4, “affected_region”: “Southern Red Sea / Bab el-Mandeb”, “source_reliability”: “verified”, “carrier_advisory_issued”: true, “recommended_action”: “escalate”, “confidence”: 0.87 }
That confidence score matters. I’ve sat in enough crisis calls where someone forwards a tweet and suddenly the whole team is scrambling - only to find out it was a recycled report from three weeks ago. An unverified social media report gets a low confidence. A confirmed carrier advisory with vessel rerouting data gets a high one. The Reporter uses this to calibrate - a severity-2 unverified report gets a yellow notification. A severity-4 confirmed escalation gets a red alert with an “Escalate to VP” button.
This is the difference between “something happened in the Red Sea” and “your container MSCU7234561 on MSC IRINA is now in a severity-4 zone with a confirmed carrier advisory - here are your three options.”
What this costs
Eleven euros a month.
For a system that monitors vessel positions every 30 minutes, classifies geopolitical risk with AI, matches threats to specific cargo records, and delivers actionable alerts to your phone.
I’m not saying this replaces a full TMS or a visibility platform like project44 or FourKites. Those do far more - booking, documentation, carrier integration, customs. But if your specific need is “tell me when my cargo is in danger during a geopolitical crisis,” you don’t need a $100K platform. You need five agents and a Telegram bot.
The stack runs on Docker Compose. No contracts. No per-user licensing. No “let me loop in our solutions architect.”
What I’m still figuring out
Sonar currently polls AIS positions every 30 minutes. That’s deliberate - it keeps API costs near zero and reduces noise. But for genuinely fast-moving situations, 30 minutes is a long time. I’m looking at aisstream.io’s WebSocket feed for real-time position streaming, triggered only when a vessel is already inside a risk zone.
The Telegram interface works beautifully for a single operator. But the moment you have a team - a duty desk with shift handovers - you need message threading, read receipts, escalation chains. I’m considering whether a lightweight dashboard makes sense, or whether Telegram groups with role-based command access are enough.
The historical context layer is the most interesting part to me. Every crisis event gets archived as a vector embedding. Over time, the Analyst can say “this situation resembles the November 2024 Red Sea escalation, which resolved in 72 hours.” That pattern recognition is where the real value compounds - but I haven’t run it long enough to see it work at scale.
Still working through that thesis. Curious if you’ve hit the same wall.